In today's digital/online/virtual age, our personal/identifiable/sensitive information is more vulnerable/exposed/at risk than ever before. Identity/ID/Personal data theft is a growing threat/concern/issue, and it can have devastating/severe/harmful consequences for victims/individuals/people.
To shield/protect/safeguard yourself from this danger/risk/hazard, it's crucial to implement/adopt/establish strong security/safety/defense measures. This includes:
* **Using/Employing/Leveraging Strong Passwords:** Create/Develop/Compose unique and complex passwords for each of your accounts/profiles/online services. Avoid using/reusing/repeating the same password across multiple platforms.
* **Enabling/Activating/Turning On Two-Factor Authentication (copyright):** copyright adds an extra layer of protection/security/safety by requiring a code from your phone or email in addition to your password.
* **Monitoring/Tracking/Reviewing Your Credit Report:** Check your credit report regularly for any suspicious/unusual/unfamiliar activity.
* **Being/Remaining/Staying Vigilant Online:** Be cautious about sharing personal/private/sensitive information online, and avoid/steer clear of/stay away from phishing scams.
Entering the Labyrinth: Grasping copyright Laws and Penalties
Navigating the world of proofs can be a complex affair, especially when it comes to improperly documents. Regulations surrounding copyright are strict, and the penalties can be grave. Before thinking about to possess a copyright, it's essential to thoroughly grasp the judicial repercussions.
- Owning a copyright can conclude in fines
- Jail time is a potential outcome
- Criminal records can impact your future
Keep in mind that the risks of utilizing a copyright far exceed any possible benefits.
The Evolution Beyond Passwords: The Rise of Biometric Security in Identity Protection
In a world increasingly reliant on digital interactions, the traditional password is facing growing scrutiny. Vulnerabilities in password systems, coupled with rising concerns about data breaches, have spurred a rapid shift towards more robust and secure identity confirmation methods. Biometric security, leveraging unique biological traits for authentication, is rapidly emerging as the preferred solution in this evolution.
Biometrics offers several strengths over traditional passwords. Its inherent uniqueness makes it far more difficult to replicate. Unlike passwords, which can be forgotten, biometric traits are inherent to an individual. This inherent security stems from the fact that these traits are difficult to alter, providing a significantly higher level of protection against unauthorized access.
The implementation of biometric systems has seen significant increases across various sectors. From smartphones unlocking with fingerprint scans to airports utilizing facial recognition for border control, biometrics is finding its place in our daily lives.
- Popular biometric modalities include fingerprint scanning, iris recognition, facial recognition, and voice authentication.
- Continuous advancements in sensor technology and artificial intelligence are further enhancing the accuracy and reliability of biometric systems.
While biometric security presents a promising future for identity protection, it is essential to address concerns regarding privacy. Transparent data handling practices and strict regulatory frameworks are crucial to ensuring that the benefits of biometrics are realized without compromising individual liberties.
Verifying Identities in a Digital Age: Innovative Technology Solutions
In our increasingly virtual realm, securely authenticating identities has become paramount. Traditional methods often prove insufficient in the face of evolving threats. Fortunately, innovative approaches are emerging to bolster security and mitigate fraud.
These advancements encompass a range of techniques, including biometrics, blockchain, and artificial intelligence. Biometric authentication leverages unique physical or behavioral traits for robust identification. Blockchain offers an immutable ledger to track identity information, ensuring its integrity and transparency. AI-powered systems can analyze vast datasets to detect patterns indicative of fraudulent activity.
The integration of these technologies holds the potential to revolutionize how we manage identities in the digital age. By embracing innovation, we can create a more trustworthy online environment for all.
The Evolving Landscape of Identity Theft: Strategies for Mitigation
In today's virtual landscape, identity theft Underage access to alcohol presents a escalating threat. Criminals are regularly evolving their tactics to exploit vulnerabilities and gain sensitive personal information. To minimize the risk of becoming a victim, individuals must adopt multi-faceted strategies. This includes adopting strong passwords, activating multi-factor authentication, scrutinizing financial accounts for suspicious activity, and educating oneself about the latest fraudulent practices. By remaining vigilant and taking protective measures, individuals can bolster their defenses against identity theft.
Here are crucial to remember:
* Exercise vigilance when sharing personal information online or over the phone.
* Review credit reports regularly for any discrepancies.
* Report any suspected cases of identity theft to authorities promptly.
Through adopting these approaches, individuals can effectively counter the evolving threat of identity theft.
Securing Your Data, Ensuring Your Future: A Comprehensive Approach to Identity Verification
In today's digitally driven world, safeguarding your sensitive data is paramount. Identity verification has become a crucial foundation of online security, ensuring that only legitimate users have access to platforms. A comprehensive approach to identity verification involves multiple layers, ranging from strong authentication methods like multi-factor authentication to pattern recognition technologies.
With implementing robust policies, organizations can minimize the risk of data breaches and fraudulent activity. Moreover, staying informed about emerging threats and security guidelines is essential for individuals to protect their digital identities.
- Implementing multi-factor authentication (MFA) adds an extra layer of security by requiring users to provide multiple forms of identification.
- Behavioral technologies use unique identifiers to verify identity, such as fingerprint scans or voice recognition.
- Training yourself about online security threats and best practices is crucial for protecting your data.
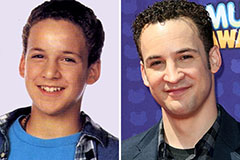 Ben Savage Then & Now!
Ben Savage Then & Now! Michael Oliver Then & Now!
Michael Oliver Then & Now! Talia Balsam Then & Now!
Talia Balsam Then & Now! Marcus Jordan Then & Now!
Marcus Jordan Then & Now! Tina Louise Then & Now!
Tina Louise Then & Now!